Technology Innovation Institute’s (TII) Secure Systems Research Center (SSRC) has joined the Confidential Computing Consortium (CCC), a project community at the Linux Foundation, dedicated to defining and accelerating the adoption of confidential computing.
The CCC brings together hardware vendors, cloud providers, and software developers to accelerate the adoption of Trusted Execution Environment (TEE) technologies and standards.
Embodying open governance and collaboration, the project community protects in-use data through computation in a hardware-based Trusted Execution Environment. These secure and isolated environments prevent unauthorized access or modification of applications and data while in use, thereby increasing the security assurances for organizations that manage sensitive and regulated data.
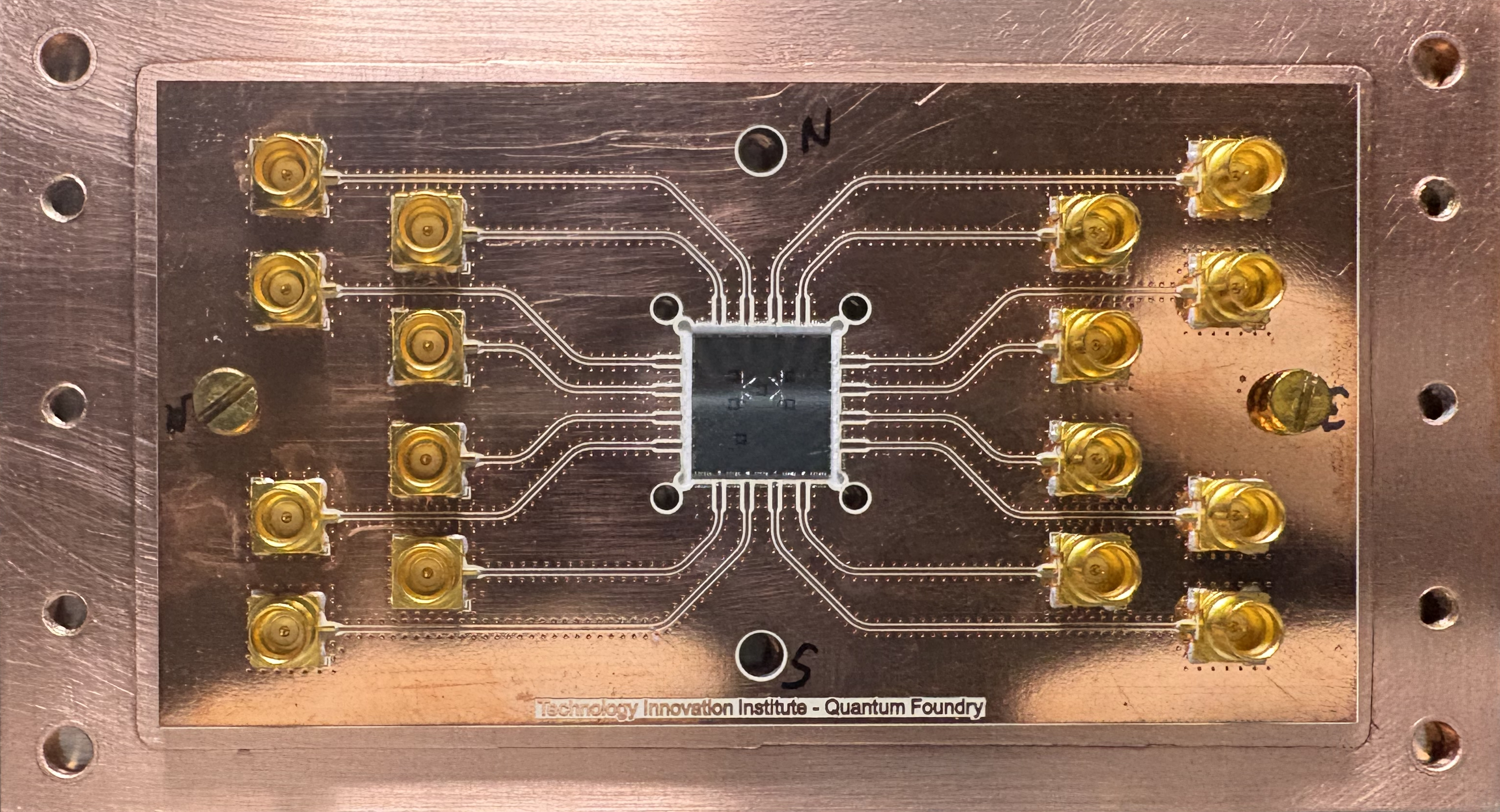
SSRC’s membership to the CCC will enable the Center to deliver breakthroughs in applied research in cyber-physical systems’ security to ensure transformative outcomes.
Dr. Ray O. Johnson, Chief Executive Officer of Technology Innovation Institute, said: “TII is delighted to see the Secure Systems Research Center become a working member of the Confidential Computing Consortium. This is a major step in the Center’s mission, to drive end-to-end security and resilience in cyber physical and autonomous systems. We often notice data are encrypted at rest in storage and while transiting across the network, but not while in use. This ability to protect data in use, though crucial, is limited in conventional computing infrastructure.”
Dr. Shreekant “Ticky” Thakkar, Chief Researcher, SSRC, said: “The Confidential Computing Consortium is standardizing hardware level security capabilities in Silicon, and this helps to establish security at the lowest level in a system. By providing security though the lowest layers of hardware, with minimal dependencies, it is possible to establish a strong security foundation to build the remaining software stack on top – thereby reducing exposure to potential compromise at any point in the system lifecycle. Our role is to contribute to this effort so that we can leverage a uniform mechanism with our secure RISC-V based solution for drones and communication devices.”